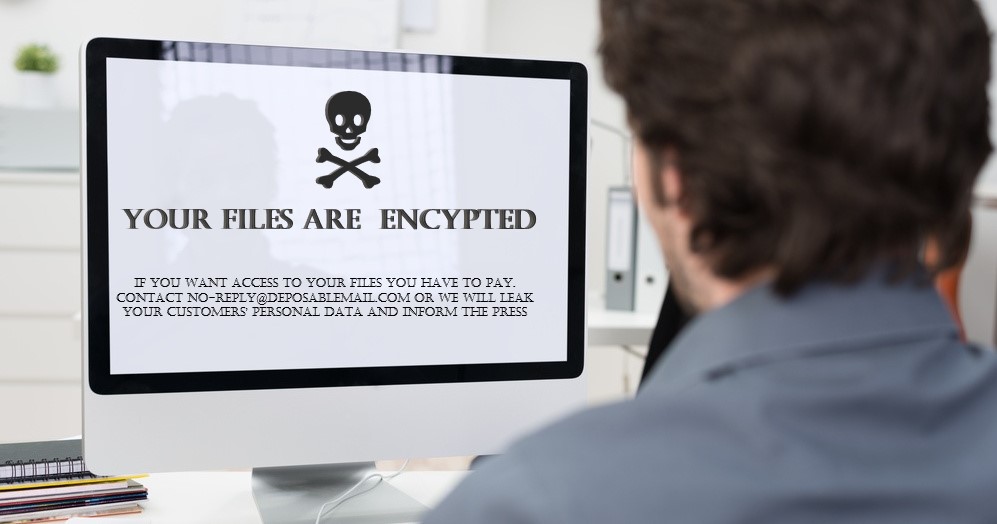
In the cybersecurity industry, ransomware has been the story of the past few years. Despite being around for over a decade or more, attacks leveraging the malware really spiked during the pandemic. It continues to run wild thanks to a perfect storm of sub-par corporate security, highly accessible ransomware-as-a-service (RaaS) offerings on the dark web, and hostile nations prepared to shield criminal actors.
Data increasingly lies at the heart of the threat. It’s now typically exfiltrated before being encrypted by threat actors, offering a double opportunity for ransom and monetization. But if organizations protect that data first by scrambling it, they can proactively limit the damage that could be done. According to one study, use of high-grade encryption is one of the top three ways to mitigate the cost of a breach.
Driven by RaaS
Ransomware has come a long way from the first ever recorded attack, back in 1989, when floppy disks distributed at an AIDS conference were installed with a file-encrypting trojan. Consumers were for many years the main target for ransomware actors, before it became clear that businesses were both vulnerable to compromise and willing to pay a higher ransom. From the second half of the 2010s, attacks have soared. According to FBI figures, the costs associated with ransomware surged 449% between 2019 and 2021. And the number of reports to the authorities increased 109% from 2017 to 2021.
New research highlights the continued threat over the past year. With organizations distracted, home workers potentially less secured and remote infrastructure exposed, attackers have had a field day. It reveals that 66% of organizations were hit by ransomware in the past year, up from 37% in 2020—a 78% increase. Why the dramatic surge in attacks? A large part of it can be attributed to RaaS and the affiliate model. Here, cybercrime “affiliate” groups pay the ransomware developer a monthly fee in return for an 80% cut of any profits. Because it’s so easy to use, RaaS has provided ransomware to a new breed of criminals—perhaps less technically proficient but no less avaricious.
The double extortion threat
According to a 2021 report from Verizon, ransomware appeared in 10% of data breaches over the previous year, more than double the figure of 12 months earlier. That’s because most attacks now feature a data theft element in order to force payment. The report claimed ransomware increased by 6% year-on-year and is now the third most common “action” leading to breaches.
Data exfiltration or “double extortion” is now said to feature in 84% of attacks. It can create major financial and reputational risk for victim organizations—either if regulated employee/customer personal data is stolen or if sensitive IP goes missing. Big-name tech brands including Apple and Nvidia appear to have been caught out in the past.
Threat actors typically put a sample of the stolen data on a leak site, promising to release more if the ransom isn’t paid. But even paying up is no guarantee that the data will be deleted. The impact of such data loss could include:
- Legal costs (including class action lawsuits)
- Regulatory fines
- Ransom (now $812,360 on average)
- Loss of competitive advantage
- Customer churn/reputational damage
- Cost of investigation, remediation and clean-up
Data-centric security
The best course of action is of course to stop a ransomware attack from happening in the first place. Various best practices including regular patching, multi-factor authentication, phishing awareness training and network monitoring tools can help to prevent initial access or spot a breach early on before data has been taken and encrypted.
But these are far from fool proof, and attackers are innovating and growing in number all the time. The most successful groups have millions to spend on R&D and are even considering hiring zero-day exploits for which there are no known patches. This is where a data-centric security strategy comes in.
Data-centric security is all about anonymizing data wherever and whenever it is used—with techniques such as encryption and tokenization. Thus, even if a hacker gets a hold of corporate data, they will not be able to read or exploit it. As an extra layer of protection, it helps to reduce cyber risk in the event that threats sneak past those prevention and detection-centric controls. In the worst-case scenario, if data is encrypted by attackers, it can always be restored from an offline backup. Data-centric security also ensures that the bad guys won’t be able to monetize it by threatening to leak.
No organization can be 100% ransomware-proof today. The odds still favor the attacker. But as part of a layered, best practice strategy, data-centric security can significantly minimize the impact of any incident and keep your customers' and employees' data safe, and the regulators happy.